If you’re concerned about backdoors, you heard about backdoors in the news and want to know what the deal is, or you have a backdoor
Working From Home…?? Are You Safe…?
The Coronavirus is hitting hard on the world’s economy, creating a high volume of uncertainty within organizations. To many, the current situation presented by the
10 Cool Gadget under Rs 5000 for Techie
While most of you may have already finished buying gadgets in the end season sale, I m sure some of you are still thinking
Fingerprint vs Pin vs Password: The safest way to lock your phone
With the amount of personal data, we keep on our phones, security is essential. If you think about it, our smartphones hold so much information
8 Easy Ways to Speed Up Your Internet Connection
Internet connections could always be faster. Whether your downloads are crawling, streaming feels like a slideshow, or you just want to maximize your speeds, here’s
5 Apps to Get More From Your Android’s Physical Buttons
1) Button Mapper Button Mapper is a comprehensive app that can remap any button your phone or connected accessory has. It’s capable of personalizing the
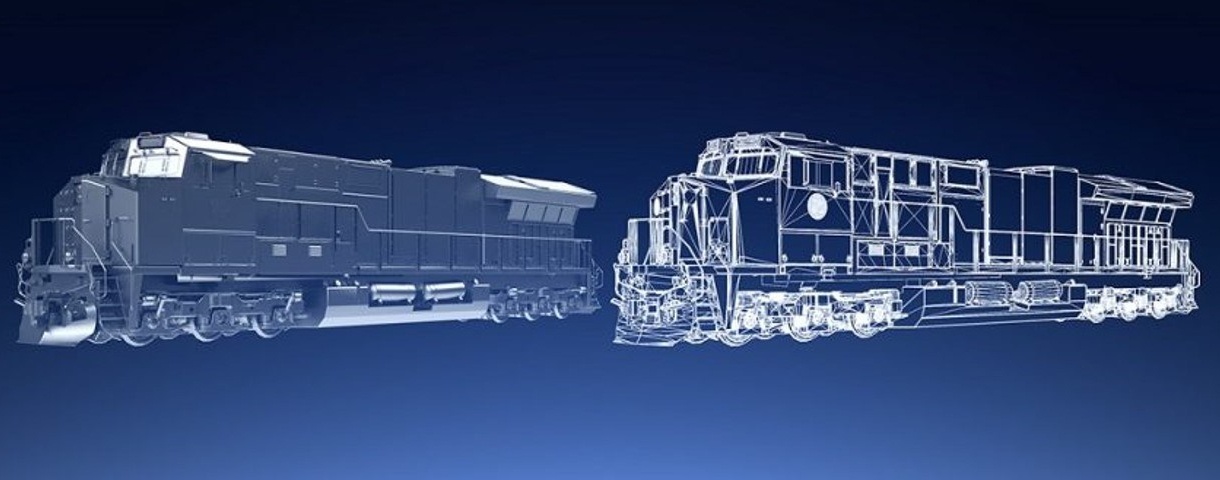
What Is Digital Twin Technology And Why It Is Important For Industry ?
A digital twin is a cross-domain digital model that precisely denotes a product or performance of a product in operation.The digital twin evolves and continuously
Gmail encryption: Everything you need to know
Sending an unencrypted email is often likened to a postcard, in that anyone who wants to read it just needs to look at it. Obviously
The 25 Worst Passwords of 2018.Is yours on this list?
Despite warnings by security experts and repeated breaches, it appears that some internet users have not updated their passwords to a more secure one. SplashData,
What is Overclocking, How It Works and What You Need to Know About It ?
Overclocking is the action of increasing a component’s clock rate, running it at a higher speed than it was designed to run. This is usually